Trong vài tháng qua, khi Google triển khai Gemini Enterprise trên nhiều ngành công nghiệp…
How secure is Google Cloud Platform (GCP)?
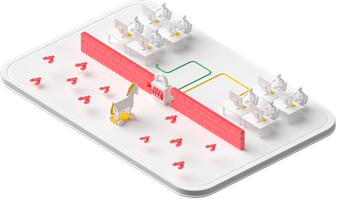
Trusted infrastructure
Google's cloud infrastructure doesn't rely on just one technology to make it secure. The Google team builds security on advanced layers of protection to deliver full depth protection. This is also one of the reasons Google Cloud Platform – GCP is the first choice of businesses.
Multi-layer security
Device operation & security
Google develops and deploys software systems using strict security procedures. Google operations teams detect and respond to threats to the system base from insiders and outsiders 24/7/365
Communication on the Internet
Communication over the internet in Google's public cloud service is encrypted in transit. Google's network and systems have many layers of security to protect customers from DoS attacks.
Identification
Identity, user, and service will pass through stronger authentication than multiple layers of security. Access to important data will be secured by advanced technology like an anti-phishing security key.

Hosting Service
Data stored in Google's IT systems is automatically encrypted and distributed for availability and trust. This will help guard against unauthorized access and service interruptions
System deployment
All applications that run on Google's system base are implemented with an element of security in them. Google makes no assumptions about trust between services, and Google uses a variety of mechanisms to establish and maintain trust. Google's system base is designed to be multi-user from the ground up.

Hardware system base
From the physical system base to purpose-built servers, networking gear, and on-demand security chips to low-level software packages to run on multiple machines. The entire hardware system base is Google controlled, secured, built, and upgraded.

Source: Gimasys